User Activity Documentation Linked to Keevee1999 and Alerts Logs
User activity documentation is increasingly recognized as vital in cybersecurity. Influenced by thought leaders like Keevee1999, organizations are adopting systematic tracking methods. This practice enhances transparency and accountability. Alerts logs play a crucial role in monitoring user behavior, allowing for rapid identification of anomalies. As organizations refine their strategies, the relationship between documentation and alerts becomes increasingly intricate, raising important questions about their collective impact on security measures. What implications does this have for future cybersecurity practices?
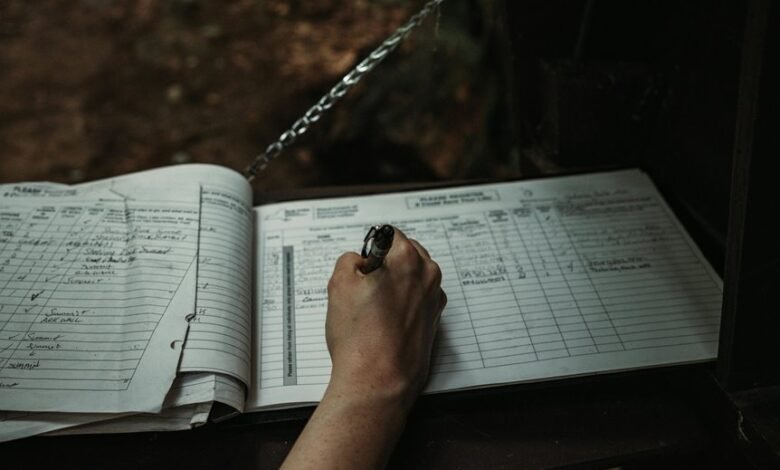
The Importance of User Activity Documentation
Although often overlooked, user activity documentation plays a crucial role in understanding user behavior and optimizing system performance.
By implementing robust activity tracking, organizations enhance user accountability, ensuring that actions are logged and monitored. This transparency fosters responsible usage while providing insights into system interactions.
Ultimately, thorough documentation empowers users and administrators alike, leading to improved efficiency and informed decision-making within digital environments.
Analyzing Keevee1999’s Influence on Cybersecurity Practices
As cybersecurity continues to evolve, the influence of individuals like Keevee1999 on best practices and community standards becomes increasingly significant.
Keevee1999’s contributions have shaped emerging cybersecurity trends, emphasizing proactive measures and collaborative defense strategies. By advocating for transparency and user education, Keevee1999 has fostered a culture of vigilance, encouraging a collective approach to enhancing security that empowers individuals and organizations alike.
Understanding Alerts Logs and Their Role in User Monitoring
The insights gained from community advocates like Keevee1999 highlight the importance of comprehensive monitoring tools in cybersecurity frameworks.
Alerts logs serve as vital instruments for assessing user behavior, facilitating effective alert classification. By categorizing alerts based on user activities, organizations can swiftly identify anomalies and potential threats, thereby enhancing their security posture while respecting user freedoms and privacy considerations.
Best Practices for Enhancing Security Through Documentation and Alerts
In order to bolster security measures, organizations must prioritize meticulous documentation and effective alert management.
Adhering to established documentation standards enhances transparency and accountability, while robust alert systems ensure timely responses to potential threats.
Conclusion
In conclusion, the integration of user activity documentation, influenced by thought leaders like Keevee1999, significantly enhances organizational cybersecurity. By leveraging alerts logs, organizations can quickly identify anomalies, fostering a culture of vigilance. Notably, a study found that organizations with comprehensive documentation practices can reduce incident response times by up to 50%. This statistic underscores the necessity of adopting best practices in user monitoring to bolster security measures effectively, ultimately leading to informed decision-making and a stronger defense strategy.