Network Activity Overview Linked to 1zy549vdwefaqwd54670 and Monitoring Notes

The unique identifier 1zy549vdwefaqwd54670 serves as a pivotal reference in the analysis of network activity. Its role in tracking data packets allows for a detailed examination of traffic patterns and bandwidth utilization. By employing various monitoring techniques, organizations can identify anomalies and enhance their network management strategies. Understanding these dynamics prompts further exploration into the implications of continuous monitoring and its potential to mitigate emerging threats.
Understanding the Unique Identifier: 1zy549vdwefaqwd54670
The unique identifier 1zy549vdwefaqwd54670 serves as a critical component in network activity monitoring, functioning as a distinct reference point for tracking and analyzing data packets.
Its identifier significance lies in its ability to provide unique functionality that enhances data integrity and accuracy.
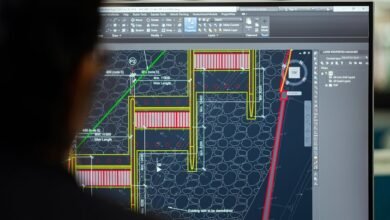
Analyzing Network Activity Trends
While assessing network activity trends, analysts must consider data patterns that emerge over time, as these patterns can reveal underlying issues or opportunities for optimization.
By examining network traffic, analysts can identify fluctuations and anomalies, allowing for strategic adjustments.
This analytical approach empowers organizations to enhance performance, ensuring that resources are allocated efficiently and that potential vulnerabilities are proactively addressed.
Monitoring Techniques for Enhanced Visibility
Effective monitoring techniques are essential for achieving enhanced visibility into network performance and security.
Packet capture allows for the collection of data packets traversing the network, enabling comprehensive traffic analysis. This method reveals bandwidth usage, identifies anomalies, and facilitates troubleshooting.
Implications for Network Management Strategies
Clarity in network management strategies is paramount in navigating the complexities of modern digital environments.
Effective risk assessment enables organizations to identify vulnerabilities, while strategic resource allocation ensures optimal performance. Balancing these elements allows for a resilient network infrastructure.
Consequently, network managers must prioritize transparency and adaptability, fostering an environment where proactive measures are implemented to mitigate risks and maximize resource efficiency.
Conclusion
In the intricate web of network management, the unique identifier 1zy549vdwefaqwd54670 serves as a beacon, illuminating the pathways of data flow. Through diligent monitoring and analysis, organizations can navigate the complexities of their network landscape, identifying trends and potential threats with precision. By leveraging effective techniques, they not only enhance their operational efficiency but also fortify their defenses against emerging risks. Ultimately, this proactive approach transforms uncertainty into opportunity, ensuring a resilient network environment.